This year marks the tenth anniversary of the Microsoft Bug Bounty Program, an essential part of our proactive strategy to protect customers from security threats. Since its inception in 2013, Microsoft has awarded more than $60 million to thousands of security researchers from 70 countries. These individuals have discovered and reported vulnerabilities under Coordinated Vulnerability Disclosure, aiding Microsoft in navigating the continuously evolving security threat landscape and emerging technologies.
In this blog post, we will reflect on the milestones and lessons learned from the Microsoft Bug Bounty Program over the past decade, exploring both the opportunities and challenges that lie ahead. We also extend our heartful gratitude to all security researchers who have participated in the program, contributing to the enhancement of our products and services’ security for everyone. Without your creativity and collaboration, this program would not be possible. Thank you for partnering with us over the past ten years.
How it started
We inaugurated the company’s first bug bounty June 2013, launching with two programs. These targeted novel exploitation techniques in Windows 8.1 and vulnerabilities reported in Internet Explorer 11 (IE11) preview. Although not pioneers in offering monetary incentives for external parties to report software security vulnerabilities, we were among the first to incentivize the discovery of issues in beta or preview products. Our belief was that early identification and resolution of bugs, preferably before the product’s general release, is paramount in customer protection.
The bug bounty initiative was not free from internal resistance. Katie Moussouris, one of the key internal proponents of the Microsoft Bug Bounty program, recalls that company executives were uncertain about the necessity of compensating researchers for bug discoveries. Although Microsoft was receiving a steady stream of bug reports annually from around the globe, the change in stance was not straightforward. There were also concerns within the team that encouraging external researchers to hunt for bugs could inadvertently expose and exploit vulnerabilities publicly, and some feared that our services might become overwhelmed.
Prior to launching the Microsoft Bug Bounty program, Katie led an internal Microsoft effort to analyze and build a business case and influence industry standards for vulnerability disclosure. She was also the Microsoft representative who coauthored and coedited the ISO standards on vulnerability disclosure and handling processes and facilitated partnerships with researchers as a core practice of effective vendor vulnerability management. The BlueHat Prize, a defensive security contest with a $200,000 prize pool, also launched during her tenure and was a key step towards demonstrating Microsoft’s commitment to rewarding researchers for important contributions in protecting the ecosystem.
After promoting the idea of incentivizing research, including emphasizing the value of finding and fixing issues in beta to minimize urgent patches post launch, the team finally received the greenlight to move forward. The Microsoft Bug Bounty Program officially launched on June 26, 2013 and it worked. During the first 30 days of the IE11 preview period, we received and fixed several high severity vulnerabilities. This experience underscored the importance of the diverse and global external research community in identifying and reporting bugs, significantly strengthening our vulnerability response process.
Inviting external contributors to aid in identifying and reporting bugs proved to be an effective method for enhancing our vulnerability response process. The initial five years brought a wealth of insights. Travis Rhodes, then a Senior Software Security Engineering Manager, recalls that in 2014, the launch of the Online Services Bug Bounty elicited so many reports from the researcher community that MSRC was challenged to innovate on our tooling and processes to scale the Bounty Program in tandem. Armed with the necessary tools and resources, we initiated a continual program, removing any time limitations and welcoming security research submissions throughout the year.
Jason Shirk, then a Principal Security Strategist, recalls that Bug Bounty was a hot topic in 2015 and 2016, with many companies interested in starting bounty programs. We started working across the industry to help standardize the models for researchers to find higher quality bugs and stabilize the “rules of the road” for consistency across Bug Bounty at different companies. He points to “BountyCraft,” a collaborative effort across Microsoft, Google, Meta (formerly Facebook), and BugCrowd to attend major security conferences and teach security researchers how to better find and report bugs for higher payouts.
In 2017, we broadened the scope to include Windows Insider Preview, Office, Edge, and more. This affirmed our belief in the effectiveness of incentives and partnerships in bolstering customer protection, a principle that has since been integral to our security approach and ongoing learning.
Investing and expanding
In the program’s early years, we received less than 100 reports annually, with a few dozen researchers participating and a few hundred thousand dollars awarded each year. However, by 2018, the program had grown, with over a dozen programs each managed by different engineering organizations. Setting budget, targets, and operations on a product-by-product basis made sense from an engineering perspective, but it also resulted in widely varied experience for researchers reporting to Microsoft. The time taken to respond to, address, and ultimately reward findings related to a product varied greatly. In some instances, the process took a few weeks, while in other cases, it extended 6 months or more. Additionally, the award amounts differed, and the determining factors were not always transparent.
After listening and learning from researchers and internal engineering teams and hearing this feedback, in January 2019 Principal Security PM Manager Kymberlee Price and then Senior Program Manager Jarek Stanley revamped our bounty programs, beginning with Windows, Azure, and M365. We increased our investment in bug bounty researcher partnerships by raising award amounts to 2 to 10x industry average for the highest impact reports. We established clearer, publicly available guidelines for all programs to help researchers’ understanding and success. Our awards now rely on four main factors: vulnerability severity, security impact, the affected product, and completeness of the report. We also discarded long standing unwritten caveats and rules and shortened the time from submission to bounty award to under 30 days.
For example, Microsoft’s practice at the time was to refuse or reduce awards for externally reported issues already discovered by an internal team. This policy often frustrated researchers, leading many to either give up because they didn’t trust the issue was truly a duplicate, or because they began to assume that anything they’d found had already been found by Microsoft. To resolve this, we changed our policy to always award the first external reports of an eligible issue, even if it had already been found but not yet fixed by Microsoft. This was not only a step forward in trust and transparency for researchers, but it made good sense for customer security as well. Gaining insight into what external researchers can uncover is invaluable, helping prioritize fixes and invest in broader mitigation to safeguard customers.
We shifted our award criteria to prioritize objectivity and customer focus, eliminating awards based on novelty, complexity, cleverness, or other subjective measures. Recognizing that even simple bugs can pose significant threats, our restructured bounty program concentrates on customer impact, irrespective of the time or effort involved in identifying the issue.
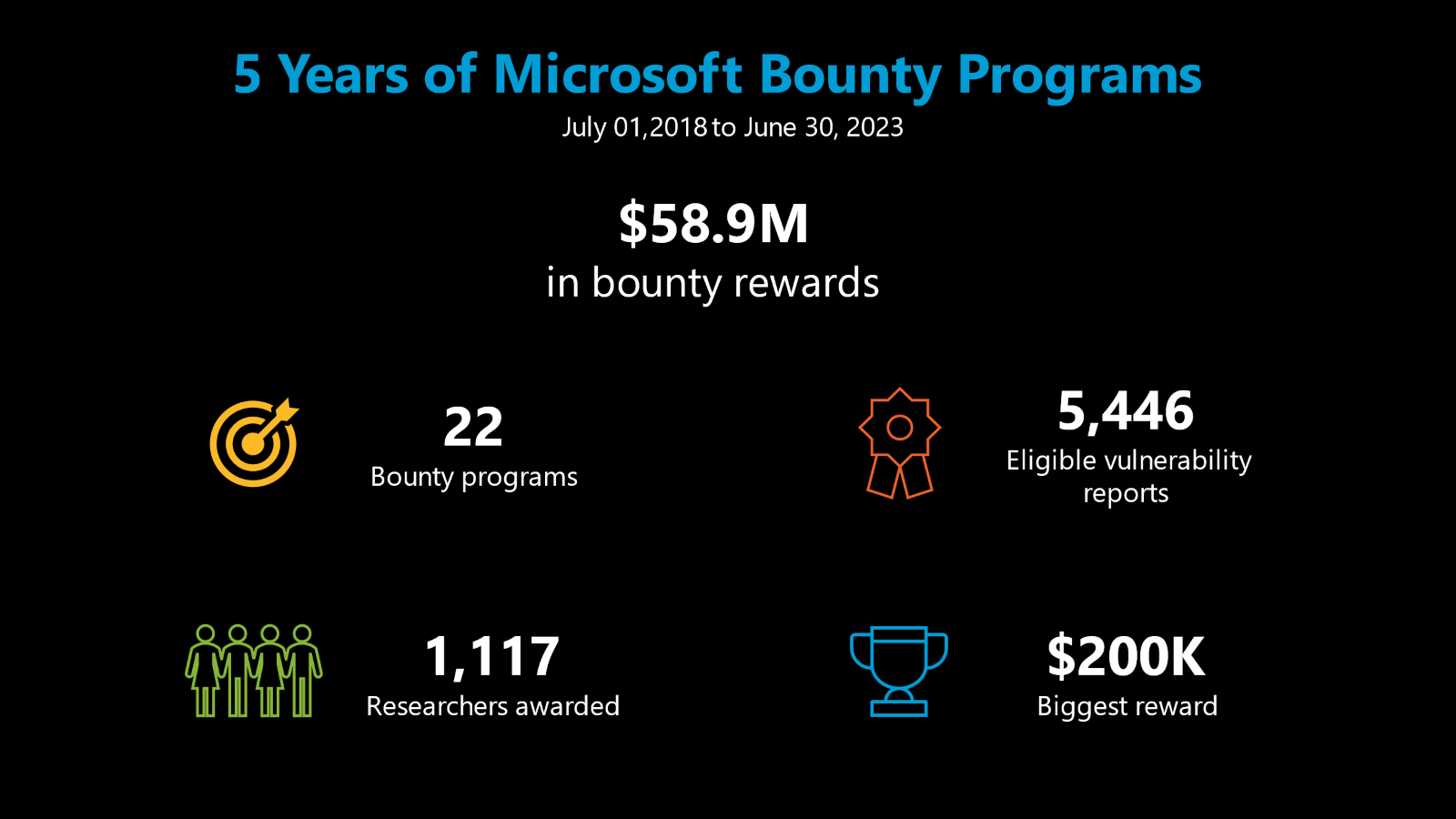
This strategy was a resounding success in rapidly scaling the bounty program. In Fiscal Year (FY) 2019, we more than doubled the number of bounty reports, program participants, and awards compared to the previous year. By FY20, we were awarding more than $13 million annually to more than 300 researchers across 15 product and service-focused programs and growing. Of the $63 million awarded since 2013, $60 million of that was allocated in the last five years alone.
Our emphasis was not solely on increasing volume but also on enhancing the severity and security impact to protect customers. In July 2020, we introduced scenario-based categories with higher awards, up to $100,000 for vulnerabilities posing serious risks to customer privacy and security. Researchers rallied, increasing the number of zero-click Remote Code Execution (RCE) or cross-tenant vulnerabilities found by more than 50% year-over-year.
But success extends beyond volume; it’s about protecting customers where it really matters and doing more than just fixing the reported bug. That’s why the data from the programs is a critical part of arming product and security teams across the company to deliver broader security improvements and mitigations beyond one-off bug fixes. For example, the Microsoft Offensive Research & Security Engineering, or MORSE, uses the vulnerabilities reported through the bounty program to help drive investment to fix them more systemically through changes to how things are done within Microsoft. The M365 Application Security team uses bug bounty data to improve and refine static analysis rules for all of Microsoft. Beyond these product team initiatives, the MSRC Vulnerability and Mitigations team conducts variant hunting as part of the case process, uncovering and reducing any related risk, leveraging the original vulnerability submitted.
Where we are today
Today, incentives and partnership are baked into our company’s vulnerability disclosure program. Every report that is triaged, assessed, and fixed is reviewed for potential bounty eligibility. There is no need to register, no need to sign up, everyone is invited. With this approach, we’ve had the pleasure of working with an incredibly diverse and talented community of researchers in over 70 countries. It’s not just part time security researchers, but also students, academics, and full-time cybersecurity professionals, including members of the offensive and defensive security teams of our Microsoft Active Protections Program partners. We even welcome the occasional teen (with permission from their parents of course).
The bounty program spans across products and services such as Azure, Edge, Microsoft 365, Dynamics 365 and Power Platform, Windows, Xbox, and more. We know there is no one-size-fits all to creative security research, so each program has its own scope, eligibility criteria, award range, and submission guidelines to help researchers pursue impactful research without causing unintended harm. These guidelines are also tailored to the specific threat model of each product or domain, to help researchers focus on areas and issues that are of the most importance to customer security.
We understand that our partnership with the community is unique and requires a tailored approach. We are constantly evolving our methods of engagement, listening, learning, and customer protection. From investment in long term research grants, focused research challenges, public thanks and recognition through our quarterly and annual Most Valuable Researcher leaderboard, we’re always listening to researchers and customer to find better ways to collaborate.
Microsoft’s partnership with the research community is one of the many ways that we protect customers. Through the bounty program, we can understand our attack surface through the researcher lens, surfacing novel and high impact vulnerabilities, and identifying opportunities for broad mitigations that lead to a holistic hardening of our attack surface. Thank you for your participation and most importantly, your diverse and unique perspectives that help us to protect our customers and empower the planet.
Aanchal Gupta, Microsoft Corporate Vice President and Deputy CISO