Hi Folks,
We want to continue to highlight changes we’ve made to our Security Update Guide. We have received a lot of feedback, much of which has been very positive. We acknowledge there have been some stability problems and we are actively working through reports of older browsers not being able to run the new application. We really appreciate your feedback as we review these issues.
We’ve heard frustrations over the removal of the previous Executive Summary section and we particularly appreciate specific examples of CVEs which needed more details in order to properly perform risk analysis on the more complex vulnerabilities. This change reflects our intentional efforts to add more information to the Frequently Asked Questions (FAQs) for certain types of CVEs over the last several years, for example:
- For Information Disclosure vulnerabilities, we incorporate “What type of information might be disclosed?”
- Office Desktop application vulnerabilities include possible Preview Pane attack vectors
- If a Group Policy _needs to be adjusted, the FAQ reflects that.
These FAQ content examples are a result of your direct feedback. Some are generated systemically for certain common types of vulnerabilities, while others are manually created for particularly unusual CVEs. We feel this strikes a good balance between providing our customers useful and actionable information while not describing the vulnerability in such detail that helps our adversaries build an exploit.
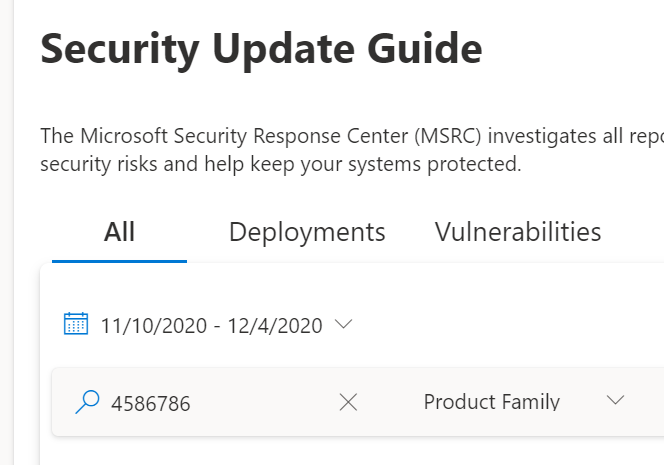
In the Security Update Guide updated design, we focus on features which provide the ability to tailor the information for a specific user’s function. We now offer three different views:
- All: A general view that shows All available information
- Deployments : The best view for people who are responsible for deploy ing updates into their environment.
- Vulnerabilities : This view focuses on the vulnerabilities and relevant information associated with each.
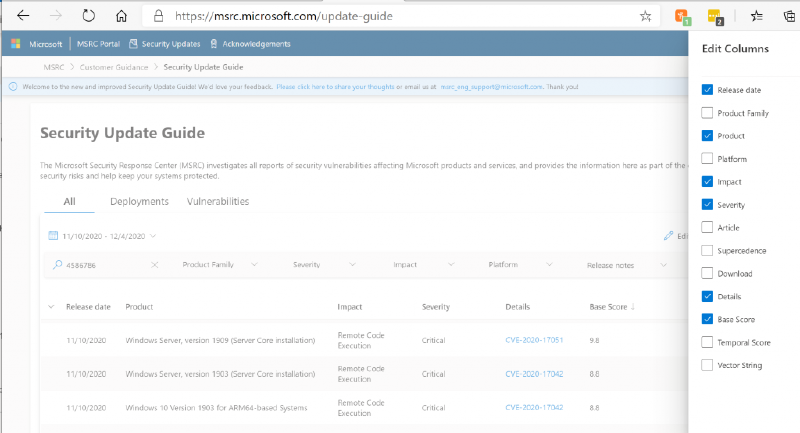
Looking more closely, each of the tabs allows you to choose which columns are displayed, and can be exported as a spreadsheet.
The “ All ” tab has access to all of the different data items and you can further filter by changing column options with the Edit Columns pane. So, for example, if you want to see the CVEs sorted by the highest CVSS base score first, you can choose to add Base Score to the grid and sort by that column.
The second tab is designed with the Deployment team in mind, where CVE information is less important. The Edit Column on this tab allows you to get a unique list of packages for the month by unselecting the Product and Platform columns. This list can be exported to Excel to setup a deployment schedule.
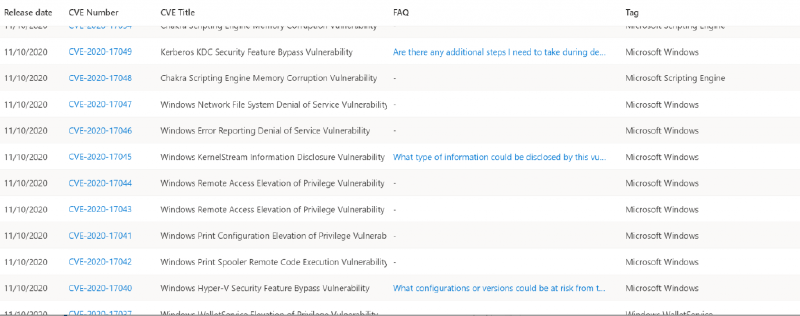
The Vulnerabilities tab puts focus on the CVEs, front and center. Here, the Edit Column include options like links to FAQs, Articles, mitigations and workarounds.
We realized that many Executive Summaries reused content which has become stale and aren’t particularly actionable, feedback indicates they aren’t often read. In every Update Tuesday, there are specific vulnerabilities which are tricky and need more information which Executive Summaries contain. That’s why we replaced the Executive Summaries with the more comprehensive CVSS scores, alongside the launch of the more flexible Security Update Guide. As the Security Update Guide now includes scoring for all CVEs, sort entries by highest severity then drill down into the provided articles for more information.
For example, let’s take three complex CVEs from November 2020:
- The FAQ for CVE-2020-17040 describes the attack vector and configurations for this vulnerability
- CVE-2020-17049raised a bunch of questions post release. We decided that an executive summary might help in this case so we added one. We also added to the list of questions in the FAQ.
- CVE-2020-17051 has an FAQ that lists the Frequently Asked Questions that we’ve received.
These changes create a platform that meet different needs across a wide range of users. Please continue to share your constructive feedback to help us make it even better!
_Lisa Olson, Senior Security Program Manager, _Microsoft Security Response Center